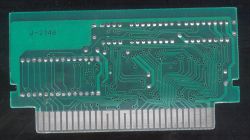
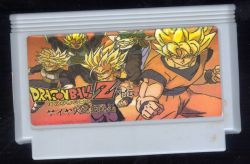
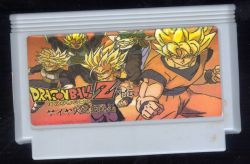
I got quite interesting pirate port of `Dragon Ball Z Gaiden - Saiya Jin Zetsumetsu Keikaku (J)`, which originally uses #16 (BANDAI 24C02) mapper.

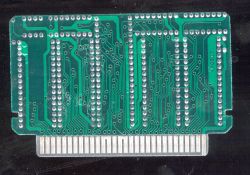
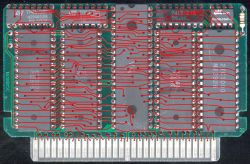
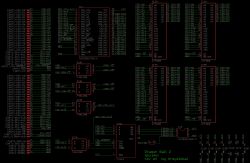
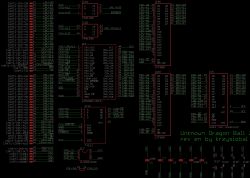
But `hackers` ported it to some custom mappers - they used VRC4 chip but connected it a little bit differently, causing two 16kB PRG banks + added few more chips to control external EPROM, which results in the following mapper:
But my question is how hackers at that time were able to hack those games? If I see at the difference between original vs pirate ROM, there are tens of places where they had to change mapper register address.
And it wasn't time where debuggers, emulators and the NES knowledge was so popular so how they know where are all the places to patch? Was it jus done automatically by searching 8DXXXX (STA $old) opcode and replacing it with `STA $new`?


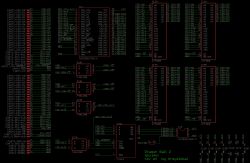
But `hackers` ported it to some custom mappers - they used VRC4 chip but connected it a little bit differently, causing two 16kB PRG banks + added few more chips to control external EPROM, which results in the following mapper:
Code:
1. Classic VRC regs (mask is 1111100000001100 / $f80c, no bus conflicts)
1.1. PRG (swap mode bit is ignored)
$8000 $c000
+-------------+-------------+
|$a000/$a004/ | -1 | [...P PPPP]
|$a008/$a00c | |
+-------------+-------------+
1.2. CHR
$0000 $0400 $0800 $0c00 $1000 $1400 $1800 $1c00
+-----+-----+-----+-----+-----+-----+-----+-----+
|$b000|$b008|$c000|$c008|$d000|$d008|$e000|$e008| [.... LLLL]
|$b004|$b00c|$c004|$c00c|$d004|$d00c|$e004|$e00c| [...H HHHH]
+-----+-----+-----+-----+-----+-----+-----+-----+
1.3. Mirroring (meaning same as on regular VRC4)
$9000, 9004, $9008, $900c:
1.4. IRQ (meaning same as on regular VRC4)
$f000: IRQ Latch, low 4 bits
$f004: IRQ Latch, high 4 bits
$f008: IRQ Control
$f00c: IRQ Acknowledge
2. Additional regs for controlling 2kB serial EEPROM (bus conflicts)
2.1. Write (only address bit matters)
A~[1...1........EEE], D~[.... ....]
|||
||+-- latch data to EPROM DI line
|+--- latch clock value
+---- latch chip enable
2.2. Read (returns value in any range where nothing is mapped, presumably $4020-$6fff)
D~[.... ...E]
|
+--------- read value from EPROM DO line
1.1. PRG (swap mode bit is ignored)
$8000 $c000
+-------------+-------------+
|$a000/$a004/ | -1 | [...P PPPP]
|$a008/$a00c | |
+-------------+-------------+
1.2. CHR
$0000 $0400 $0800 $0c00 $1000 $1400 $1800 $1c00
+-----+-----+-----+-----+-----+-----+-----+-----+
|$b000|$b008|$c000|$c008|$d000|$d008|$e000|$e008| [.... LLLL]
|$b004|$b00c|$c004|$c00c|$d004|$d00c|$e004|$e00c| [...H HHHH]
+-----+-----+-----+-----+-----+-----+-----+-----+
1.3. Mirroring (meaning same as on regular VRC4)
$9000, 9004, $9008, $900c:
1.4. IRQ (meaning same as on regular VRC4)
$f000: IRQ Latch, low 4 bits
$f004: IRQ Latch, high 4 bits
$f008: IRQ Control
$f00c: IRQ Acknowledge
2. Additional regs for controlling 2kB serial EEPROM (bus conflicts)
2.1. Write (only address bit matters)
A~[1...1........EEE], D~[.... ....]
|||
||+-- latch data to EPROM DI line
|+--- latch clock value
+---- latch chip enable
2.2. Read (returns value in any range where nothing is mapped, presumably $4020-$6fff)
D~[.... ...E]
|
+--------- read value from EPROM DO line
But my question is how hackers at that time were able to hack those games? If I see at the difference between original vs pirate ROM, there are tens of places where they had to change mapper register address.
And it wasn't time where debuggers, emulators and the NES knowledge was so popular so how they know where are all the places to patch? Was it jus done automatically by searching 8DXXXX (STA $old) opcode and replacing it with `STA $new`?